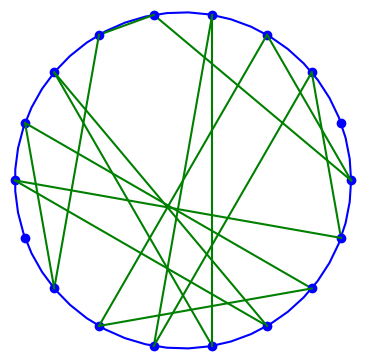
Diffie-Hellman key exchange is conceptually simple. Alice and Bob want to generate a shared cryptographic key. They want to use asymmetric (public) cryptography to share a symmetric (private) key.
The starting point is a large prime p and a generator 1 < g < p.
Alice generates a large random number x, her private key, and sends Bob gx mod p.
Similarly, Bob generates a large random number y, his private key, and sends Alice gy mod p.
Alice takes gy and raises it to her exponent x, and Bob takes gx and raises it to the exponent y. They arrive at a common key k because
k = (gy)x = (gx)y mod p.
The security of the system rests on the assumption that the discrete logarithm problem is hard, i.e. given g and gz it is computationally impractical to solve for z. This assumption appears to be true in general, but can fail when the group generated by g has exploitable structure.
You can read more about Diffie-Hellman here.
Recommended primes
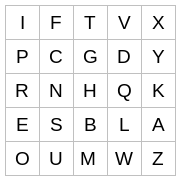
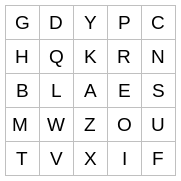
The choice of prime p and generator g can matter is subtle ways and so there are lists of standard choices that are believed to be secure.
IETF RFC 7919 recommends five standard primes. These have the form
where b is the size of p in bits, e is the base of natural logarithms, and X is the smallest such that p is a safe prime. In every case the generator is g = 2.
The values of b are 2048, 3072, 4096, 6144, and 8192. The values of X and p are given in RFC 7919, but they’re both determined by b.
I don’t imagine there’s anything special about the constant e above. I suspect it’s there to shake things up a bit in a way that doesn’t appear to be creating a back door. Another irrational number like π or φ would probably do as well, but I don’t know this for sure.
ffdhe2048
The recommended primes have names of the form “ffdhe” followed by b. For b = 2048, the corresponding value is X is 560316.
I wrote a little Python code to verify that this value of X does produce a safe prime and that smaller values of X do not.
#!/usr/bin/env python3
from sympy import isprime, E, N, floor
b = 2048
e = N(E, 1000)
c = floor(2**(b-130) * e)
d = 2**b - 2**(b-64) + 2**64*c - 1
def candidate(b, x):
p = d + 2**64*x
return p
for x in range(560316, 0, -1):
p = candidate(b, x)
if isprime(p) and isprime((p-1)//2):
print(x)
This took about an hour to run. It only printed 560316, verifying the claim in RFC 7919.
Other groups
Finite field Diffie-Hellman is so called because the integers modulo a prime form a finite field. We don’t need a field per se; we’re working in the group formed by the orbit of g within that field. Such groups need to be very large in order to provide security.
It’s possible to use Diffie-Hellman over any group for which the discrete logarithm problem is intractable, and the discrete logarithm problem is harder over elliptic curves than over finite fields. The elliptic curve groups can be smaller and provide the same level of security. Smaller groups mean smaller keys to exchange. For this reason, elliptic curve Diffie-Hellman is more commonly used than finite field Diffie-Hellman.